OneLogin
What will you learn in this topic?
By the end of this topic, you will be able to understand:
- How to configure OneLogin as a SAML SSO provider in Harness.
- How to assign users, and test OneLogin authorization.
Before you begin
- A Harness account with Account Admin permissions.
- An existing OneLogin account with admin access to create and configure applications.
You can use OneLogin as a SAML identity provider for Harness, allowing OneLogin users to log in to Harness with their existing credentials. Once configured, Harness delegates authentication to OneLogin and can optionally sync OneLogin roles to Harness user groups for automatic access control.
If you use Harness Self-Managed Enterprise Edition , your instance must be accessed via an HTTPS load balancer. SAML authentication will fail over HTTP.
To set up OneLogin as a SAML SSO provider on Harness, you exchange the necessary information between the OneLogin Harness application and Harness. The following sections cover Authentication steps, followed by Authorization steps.
OneLogin authentication on Harness
Enabling OneLogin authentication on Harness requires configuration on both platforms, as described in these sections:
Exchange Harness Consumer URL and OneLogin Metadata
-
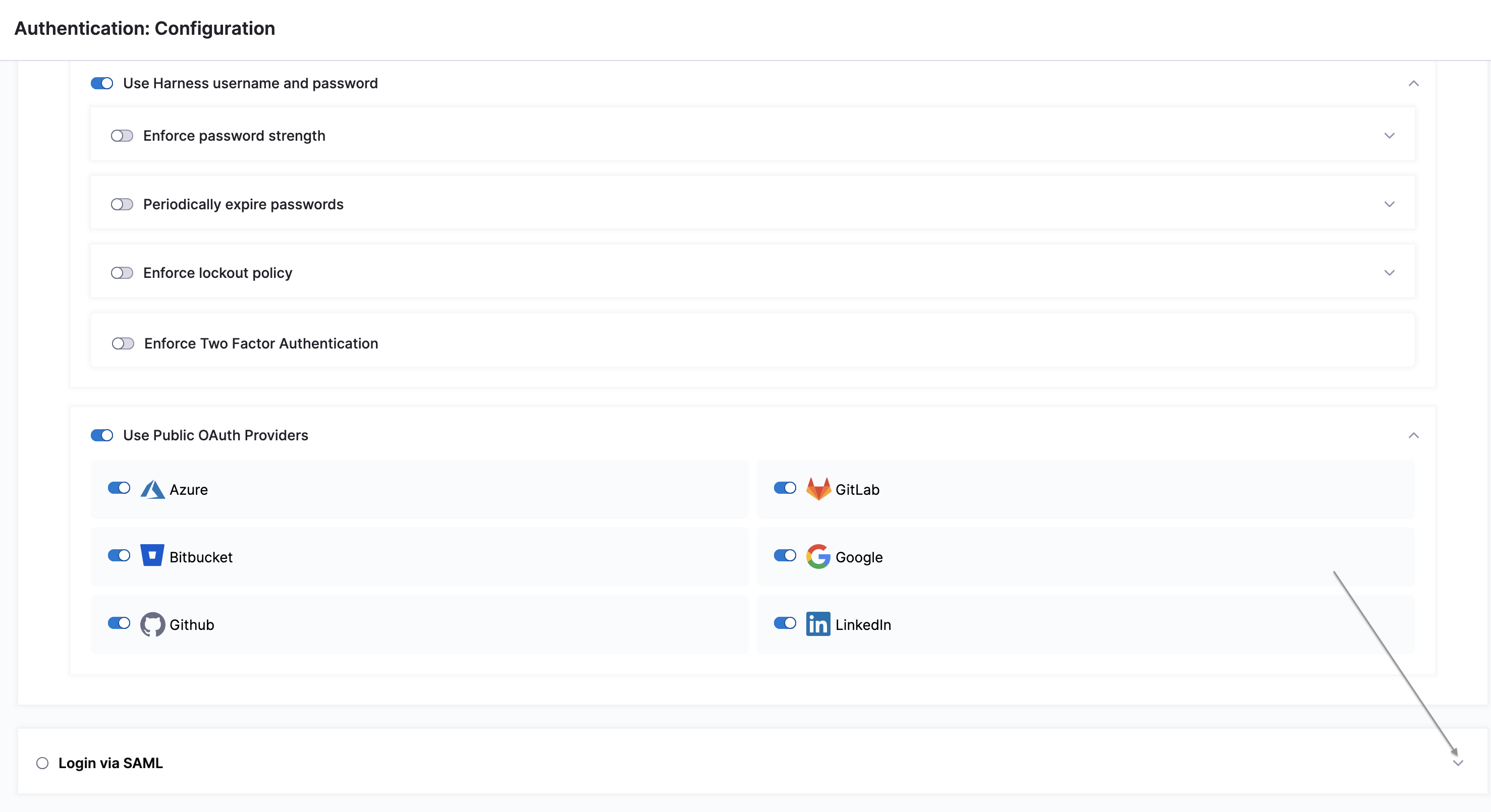
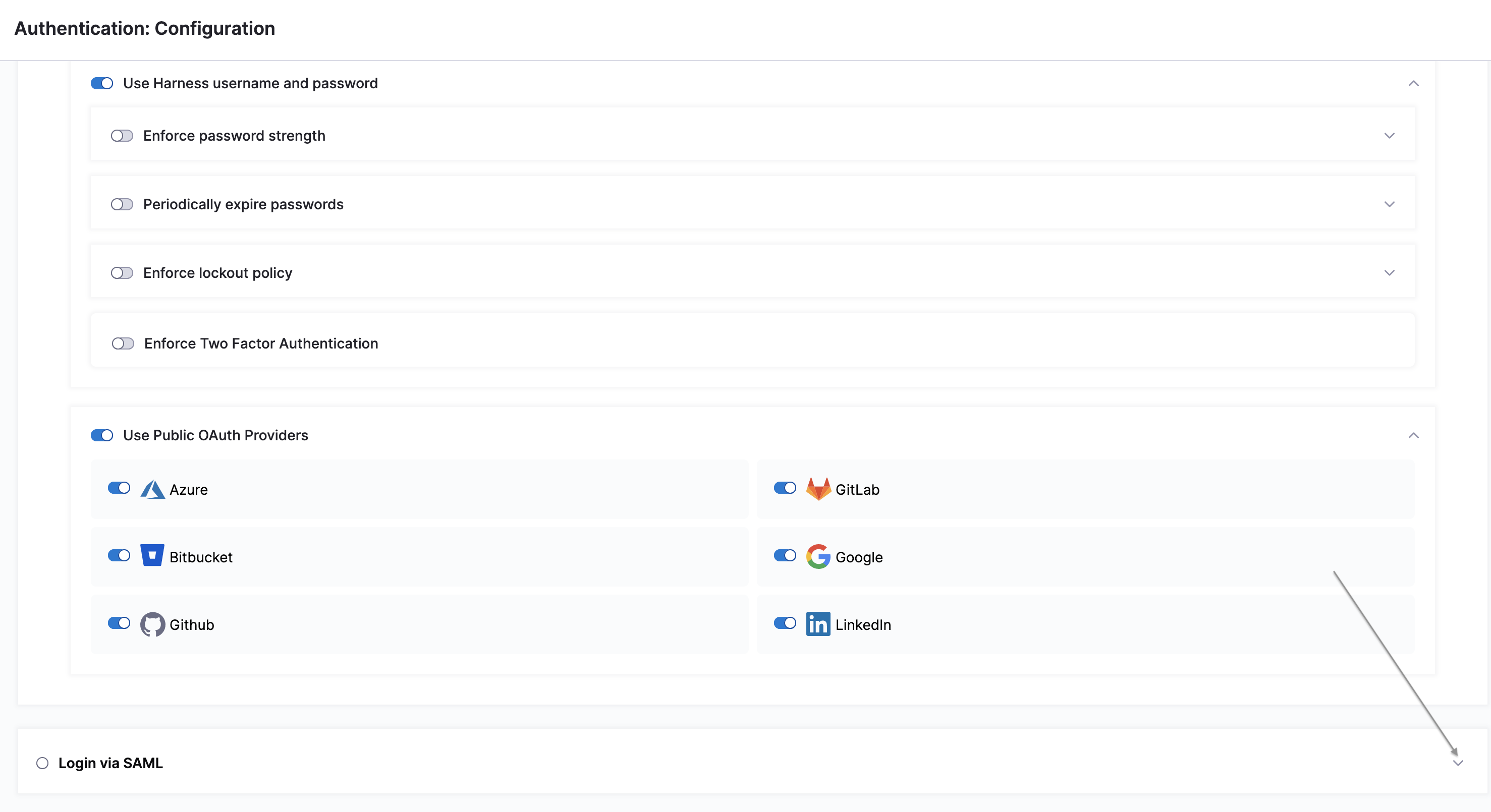
In Home, click Authentication under ACCOUNT SETUP. The Authentication: Configuration page appears.
-
Click SAML Provider. The Add SAML Provider page appears.
-
In Name, enter a name for the SAML SSO Provider.
-
Select OneLogin under Select a SAML Provider. The settings for OneLogin setup are displayed.
-
Copy the provided URL under Enter the SAML Endpoint URL, as your Harness OneLogin application's ACS URL, to clipboard.
-
In OneLogin, add the Harness app (for SaaS setup) or Harness (On Prem) app for Harness Self-Managed Enterprise Edition setup. To do so, perform the following steps:
-
Log in to OneLogin.
-
Click Administration.
-
Under the Applications tab, click Applications.
-
Click Add App.
-
Find Harness or Harness (On Prem) based on your setup, and then click the app.
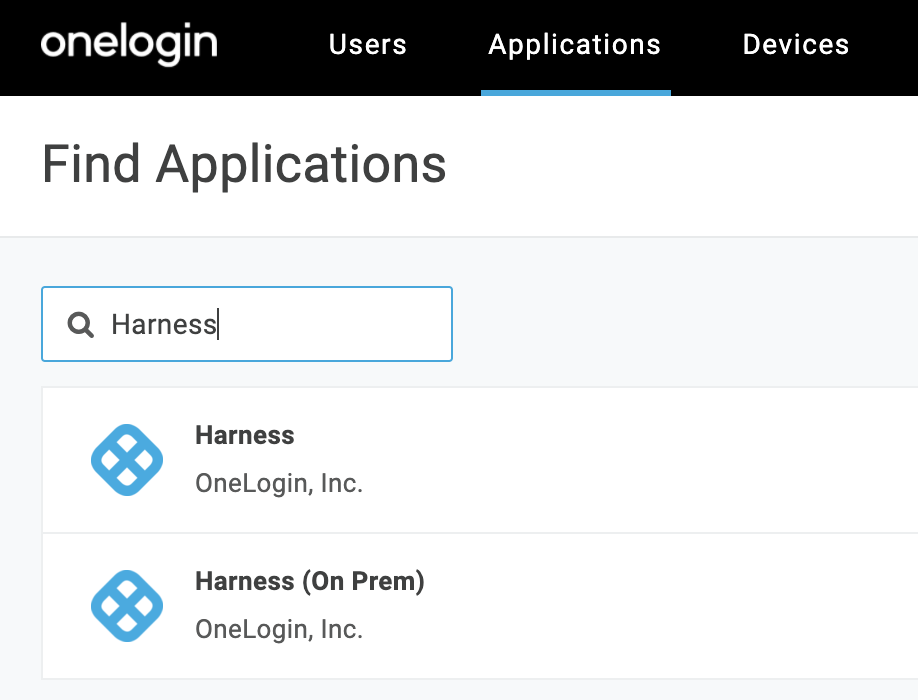
-
-
In Configuration, paste this URL into the SCIM Base URL field.
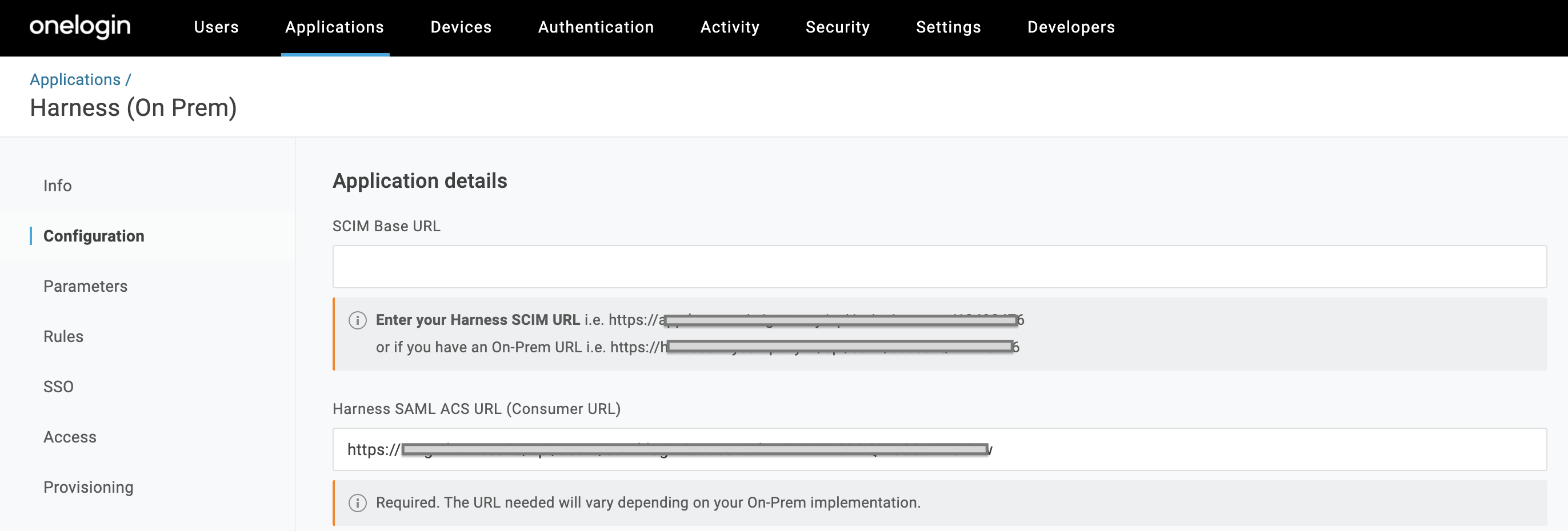
-
Skip all other Application Details fields, and click Save.
-
Navigate to OneLogin's Applications > SSO tab. At the upper right, select More Actions > SAML Metadata.
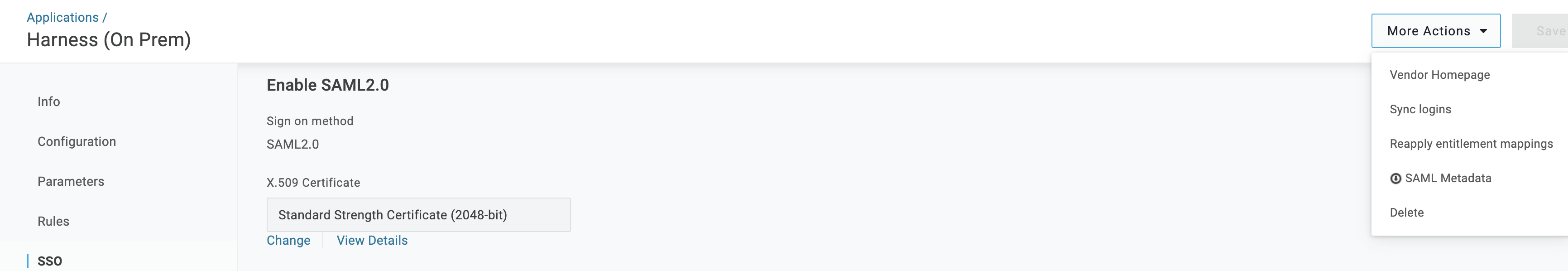
-
From the resulting dialog, download the .xml authentication file that you'll need to upload to Harness.
Assign users to roles
- In OneLogin, select Users > Users.
If you prefer to assign groups to roles, instead start at Users > Groups, and modify the following instructions accordingly.
-
Search for a user that you want to add to Harness.
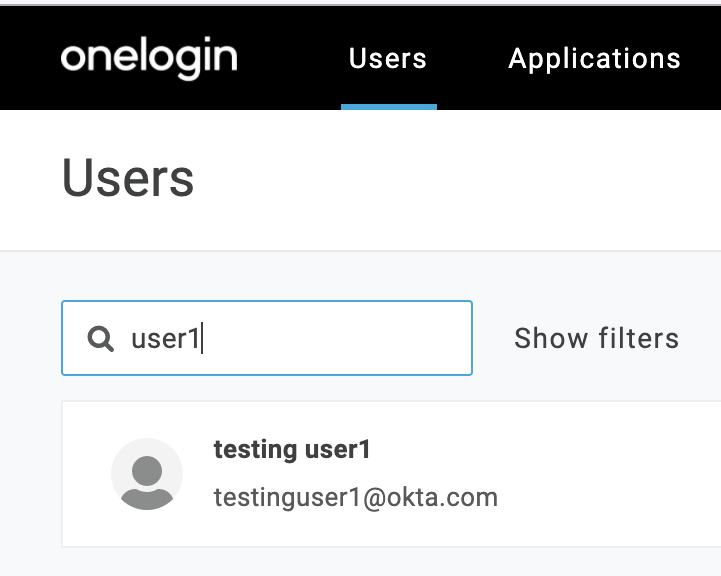
-
Click to select the user.
-
The Users page appears. Click the Applications tab.
-
Click the + button at the upper right to assign an Application.
-
Select the Application, then click Continue.
-
Repeat this section for other users (or groups) that you want to add to Harness.
Enable OneLogin as a Harness SSO provider
-
In Account Settings, select Authentication and the configuration page appears.
-
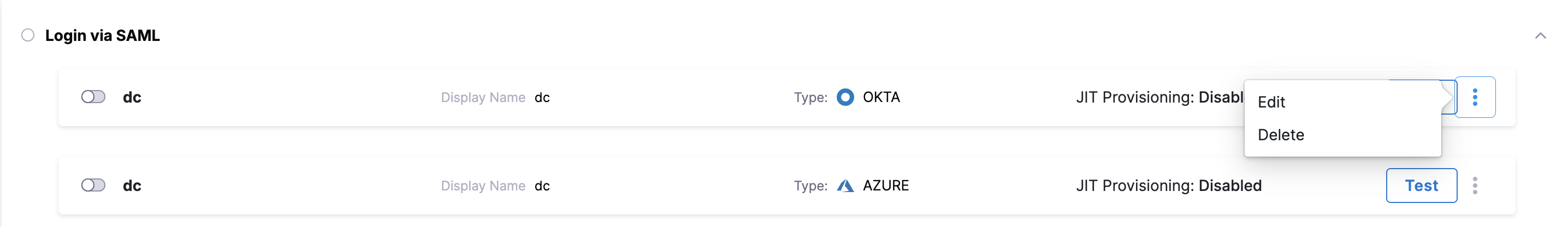
Click to expand the Login via SAML section.
-
You can see the SSO Provider you have setup listed in this section. Click the vertical ellipsis (︙) next to the SSO Provider you have set up for SSO authentication, and click Edit.
-
Use Choose File to upload the .xml file that you obtained from OneLogin.
-
Deselect Enable Authorization.
-
Select Add Entity ID and enter your custom Entity ID. The default Entity ID is app.harness.io. The value you enter here will override the default Entity ID.
-
Click Add.
-
Click Login via SAML toggle, to enable your new provider.
-
In the resulting Enable SAML Provider dialog, click TEST to verify the SAML connection you've configured.
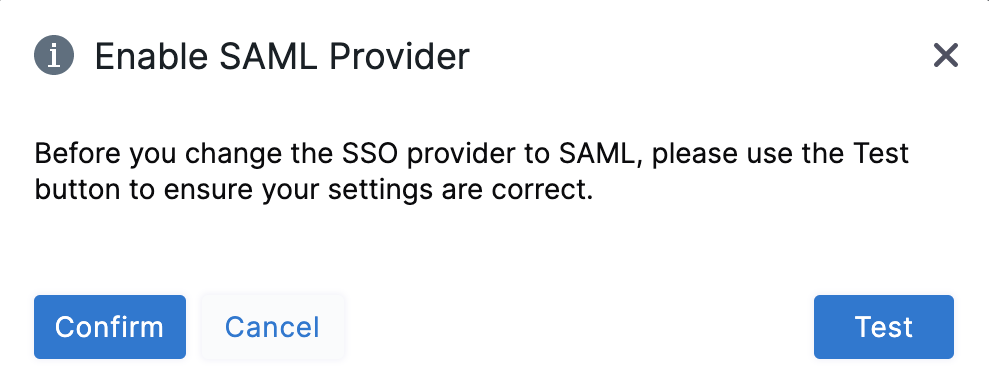
-
Once the test is successful, click Confirm to finish setting up OneLogin authentication.
OneLogin authorization on Harness
Once you've enabled OneLogin authentication on Harness, refer to the below sections to enable authorization between the two platforms:
Assign roles to users
Harness' SAML authorization replicates OneLogin Roles as Harness User Groups. Here is how to begin mapping between these entities.
- From OneLogin's, menu, select Users > Users.
- Find and select a user, assigned to Harness, to assign appropriate OneLogin Roles.
- Click the Applications tab.
- Select the specific Roles you want to assign to this user.
- Click Save User at the upper right.
- Repeat this section for other users to whom you want to assign Roles.
Define parameters
-
Select Applications > Parameters, then select the
+button to add a new Parameter. -
In the resulting New Field dialog, assign a Field name (for example Groups).
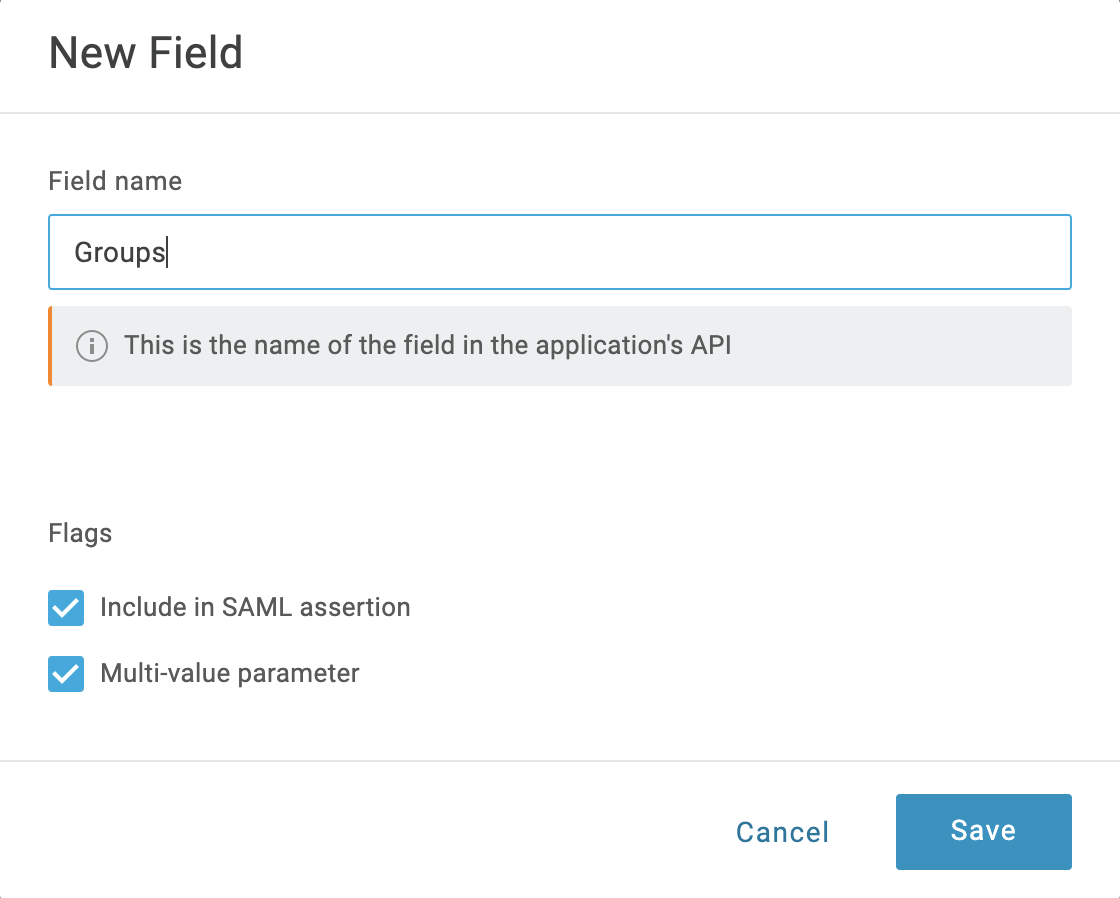
-
Select Include in SAML assertion and Multi-value parameter. Then click Save.
-
Back on the Parameters tab, select your new Groups field.
-
In the resulting Edit Field Groups dialog, set Default if no value selected to User Roles. Below that, select Semicolon Delimited input (Multi-value output). Then select Save.
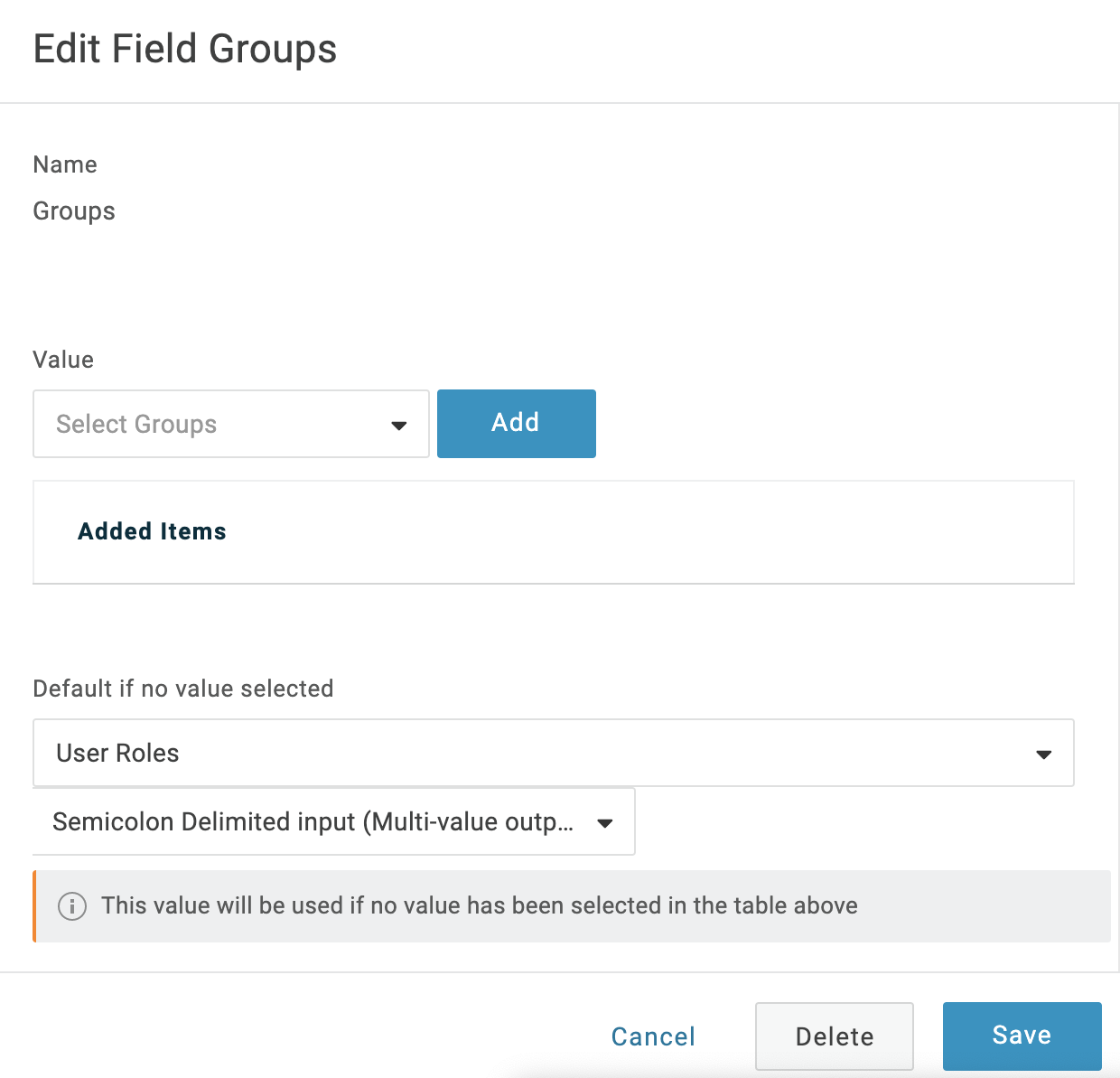
-
Select Save again at the Parameters page's upper right.
Sync users in Harness
-
In Home, click Authentication under ACCOUNT SETUP. The Authentication: Configuration page appears.
-
Click to expand the Login via SAML section.
-
You can see the SSO Provider you have set up listed in this section. Click the vertical ellipsis (︙) next to the SSO Provider you have set up for SSO authentication, and click Edit.
-
In the Edit SAML Provider dialog, click Enable Authorization.
-
In Group Attribute Name, enter the name of the Field Group you configured in OneLogin.
-
Click Save.
-
Under ACCOUNT SETUP click User Groups.
-
Click on the User Group you want to link the SAML SSO Provider to**.**
-
Click Link to SSO Provider Group.
-
In the Link to SSO Provider Group dialog, in Search SSO Settings, select the SAML SSO Provider you have set up.
-
In the Group Name, enter the name of the Field Group you configured in OneLogin.
-
Click Save.
Test the integration
After you've synced Users between OneLogin and Harness, users will be assigned to the designated Harness User Group upon your next login to Harness. To test whether OneLogin authentication and authorization on Harness are fully functional do the following:
- In Chrome, open an Incognito window, and navigate to Harness.
- Log into Harness using the email address of a Harness User that is also used in the SAML provider group linked to the Harness User Group. When the user submits their email address in Harness Manager, the user is redirected to the SAML provider to log in.
- Log into the SAML provider using the same email that the user is registered with, within Harness. Once the user logs in, the user is redirected to Harness and logged into Harness using the SAML credentials.
- In your Harness account in the other browser window, check the User Group you linked with your SAML provider. The user that logged in is now added to the User Group, receiving the authorization associated with that User Group.
You cannot delete a SAML SSO Provider from Harness that is linked to a Harness Group. You must first remove the link to the SSO Provider from the Group.